- A GDPR compliant app development guide must address consent, encryption, data rights, and third-party SDK audits – not just legal disclaimers.
- GDPR applies to any app that processes personal data of EU residents, regardless of where your company is incorporated or headquartered.
- Privacy by Design (GDPR Article 25) requires data protection to be embedded into your app’s architecture from day one, not bolted on before launch.
- Third-party SDKs, including analytics, ad networks, and crash reporters — are a leading cause of GDPR violations in mobile apps, and each must be covered by a signed Data Processing Agreement (DPA).
- Developers must build functional user rights features, including data export (CSV/JSON) and hard-delete (Right to be Forgotten) — directly into the product.

Legal Disclaimer: This guide is written by technical compliance professionals at Intigate Technologies and is intended as a technical and UX reference, not legal advice. Always consult qualified legal counsel before submitting compliance documentation or launching into EU markets.
GDPR compliance is not a documentation exercise; it is a product architecture decision.
Since GDPR came into force in 2018, cumulative fines across Europe have surpassed €7.1 billion, with €1.2 billion in penalties issued in 2025 alone. Regulators are no longer targeting only Big Tech; financial services, healthcare, and e-commerce apps are now firmly in scope.
The maximum penalty under GDPR is €20 million or 4% of global annual revenue, whichever is higher. For a growth-stage SaaS or mHealth startup, that is a company-ending number.
This GDPR compliant app development guide provides a step-by-step technical and UX roadmap — covering architecture decisions, consent mechanisms, security requirements, user rights features, and third-party SDK risks. Whether you are in pre-development planning or preparing for a compliance audit, this checklist covers every layer.
The Intigate Technologies compliance-first development team embeds GDPR requirements directly into your app’s architecture, UX flows, and data model — before a single line of production code is written.
Book a Free Compliance Architecture Review →Does GDPR Apply to Your Mobile App?
The short answer: Yes, if your app collects, stores, or processes any personal data belonging to EU residents, GDPR applies to you, regardless of whether your company is based in the EU.
This extraterritorial reach is not theoretical. The Dutch Data Protection Authority fined Clearview AI €30.5 million in September 2024 for scraping facial data without consent, and Clearview is a US-based company. TikTok received a €530 million penalty from the Irish DPC in 2025 for illegal cross-border data transfers.
What constitutes “personal data” in a mobile app?
- Obvious data: Names, email addresses, phone numbers, payment details, national ID numbers
- Hidden data: IP addresses, device IDs (IDFA/GAID), GPS coordinates, browser/app cookies, biometric data, and behavioral analytics events
Personal Data (GDPR Definition): Any information that relates to an identified or identifiable natural person, including indirect identifiers such as a device ID paired with a usage timestamp. If your app collects any of the above from EU residents, you are a data controller under GDPR and subject to its full requirements.
The Golden Rule: Privacy by Design
Privacy by Design is defined under GDPR Article 25 as the obligation to implement data protection measures both at the time of designing the processing system and by default during operation.
In practical terms, compliance cannot be a “patch” applied two weeks before app store submission. It must be part of your product requirements, data model design, API contracts, and UX wireframes from Sprint 1.
The teams at Intigate Technologies that work on Hiring a Software Development Company projects validate compliance posture before the technical architecture is finalized, not after.
Step-by-Step Guide to Developing a GDPR-Compliant App
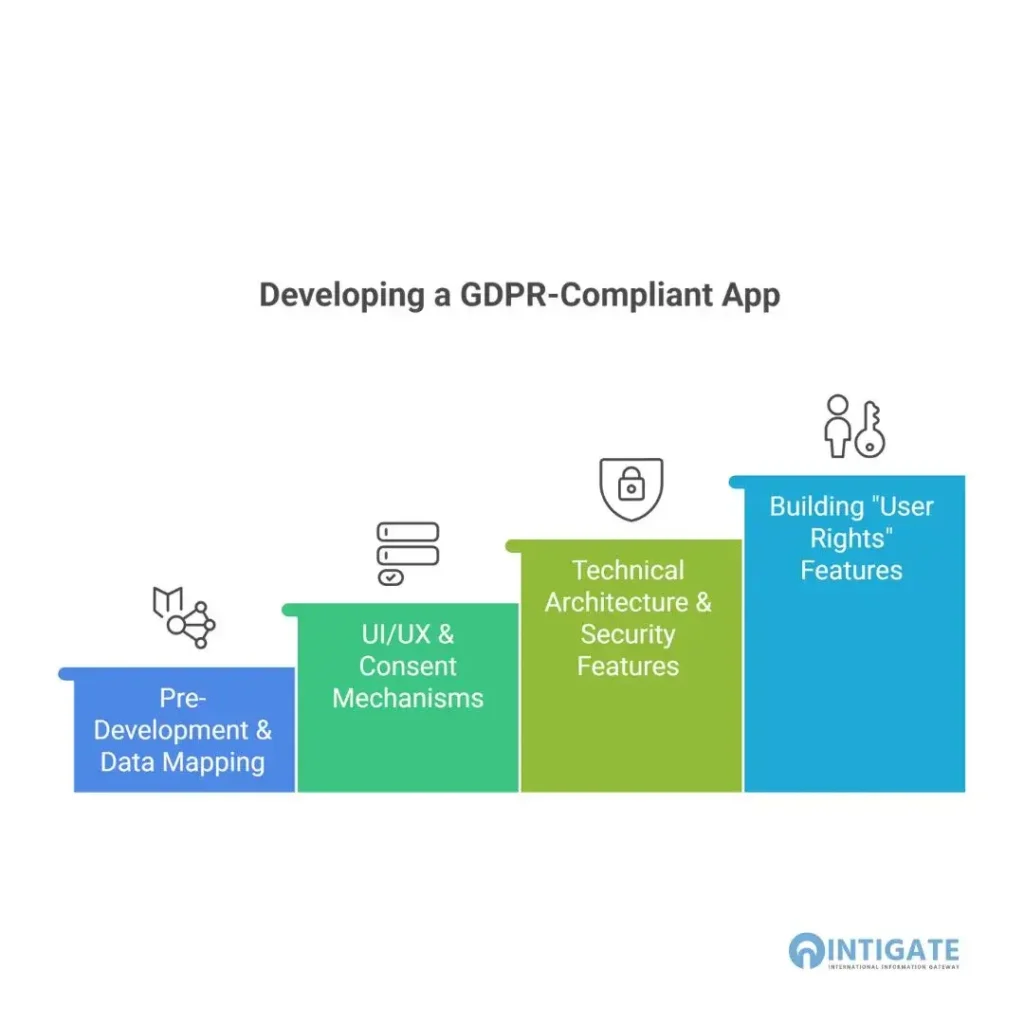
Phase 1: Pre-Development & Data Mapping
Before writing a single line of code, map every data input and output in your system.
- Conduct a Data Audit. Create a data flow diagram that traces every personal data point: where it originates (user form, device sensor, third-party API), where it is stored (app database, cloud bucket, analytics platform), and who can access it.
- Apply Data Minimization. GDPR Article 5(1)(c) requires that only data strictly necessary for the stated purpose be collected. A flashlight app has no legitimate basis for collecting location data. A food delivery app has no legitimate basis for reading contact lists.
- Define Purpose Limitation. Every data collection must have a specific, documented purpose. Data collected for order fulfillment cannot be repurposed for behavioral retargeting without a new, separate consent.
This phase directly informs how you structure your MVP Development Cost for Startups budget, compliance features are substantially cheaper to architect upfront than to retrofit after launch.
Phase 2: UI/UX & Consent Mechanisms
The most common reason apps fail GDPR audits is not a back-end data leak; it is a non-compliant consent flow in the UI.
Step 1: Require Active, Granular Consent.
GDPR Article 7 requires that consent be freely given, specific, informed, and unambiguous. This means:
- No pre-ticked checkboxes
- No consent buried in Terms & Conditions
- No bundled consent (e.g., requiring marketing opt-in to use core app features)
Granular Opt-In (definition): A consent mechanism that allows a user to independently accept or decline each distinct purpose (e.g., core app analytics vs. third-party ad targeting vs. email marketing).
Step 2: Separate T&Cs from Privacy Consent.
Your Terms of Service and your Privacy/Data Processing consent must be two distinct, separately signed documents. Combining them is a direct violation and has resulted in multi-million euro fines against major platforms.
Step 3: Implement Age Verification.
GDPR Article 8 requires parental consent for children’s data. The age threshold is 16 by default, but can be lowered to 13 by individual EU member states. If your app could reasonably attract users under 16, a verified age gate is mandatory.
Phase 3: Technical Architecture & Security Features
This is where compliance moves from policy to engineering. The following controls are non-negotiable for any GDPR-compliant app.
1. Enforce HTTPS/TLS on all communications: All data transmitted between the app and your servers must be encrypted in transit using TLS 1.2 or higher. Clear-text HTTP is not acceptable under GDPR’s security obligations (Article 32).
2. Encrypt data at rest: Personal data stored in your app’s database, cloud storage, or device-side local storage must be encrypted using AES-256 or an equivalent standard. This includes user-uploaded files, profile data, and behavioral logs.
3. Secure log management: Server and application logs must not store plain-text personal data. IP addresses, session tokens, and user identifiers in logs must be either encrypted, pseudonymized, or excluded. Accidental PII in log files has triggered multiple enforcement actions.
4. Replace security questions with MFA: “Mother’s maiden name” and “birth city” are personal data and weak authentication factors. Replace them with time-based one-time passwords (TOTP) or hardware-backed Multi-Factor Authentication (MFA).
5. Implement 72-hour breach notification procedures: GDPR Article 33 mandates that data breaches be reported to the relevant supervisory authority within 72 hours of discovery. Build an internal incident response runbook and assign ownership before launch. Daily breach notifications across Europe now average 443 per day — up 22% year-over-year.
Understanding the full scope of technical requirements is essential when estimating how long it takes to build a custom app. Compliance architecture adds meaningful but predictable scope to any development timeline.
Phase 4: Building “User Rights” Features into the App
GDPR grants data subjects eight enforceable rights. Two are the most technically demanding and most frequently overlooked by development teams.
The Right to Access & Data Portability (Articles 15–20):
Your app must allow any user to request a complete export of their personal data within 30 days of the request. The export must be provided in a machine-readable format (CSV or JSON). This requires building a data export pipeline that queries every relevant table and service, including any third-party systems where user data is stored.
The Right to be Forgotten / Data Erasure (Article 17):
This is not account deactivation. Deactivation simply flags an account as inactive while data remains in your database. GDPR’s Right to Erasure requires a hard-delete function that:
- Removes PII from your live production database
- Purges cached copies in CDN layers or application caches
- Triggers deletion in downstream third-party systems
- Schedules removal from backup snapshots within a reasonable, documented retention window
Building these features into a mature product after launch is expensive. The software maintenance cost per year impact of a retroactive compliance retrofit frequently exceeds the cost of building it correctly from the start.
The Hidden Danger: Third-Party APIs and SDKs
Most GDPR violations in mobile apps are not caused by the app developer’s own code. They are caused by third-party SDKs and APIs operating within the app without a proper consent infrastructure.
Common high-risk integrations include:
- Google Analytics / Firebase (behavioral tracking, device IDs)
- Meta Audience Network / Facebook SDK (cross-app tracking)
- Crashlytics, Sentry (may capture PII in stack traces)
- Adjust, AppsFlyer (attribution tracking, fingerprinting)
- Twilio, SendGrid (stores personal contact data externally)
Research from Usercentrics found that 90% of EU apps they analyzed were not compliant with GDPR requirements — with third-party tracking SDKs identified as the primary driver of violations.
Three mandatory steps for SDK compliance:
- Audit every SDK in your app. Review what data each SDK collects, where it sends it, and whether that transfer constitutes international data processing.
- Sign a Data Processing Agreement (DPA) with every vendor. If a vendor cannot provide a DPA, they cannot be used in your app for EU users.
- Gate SDK initialization behind consent. No analytics, advertising, or tracking SDK should initialize until the user has actively granted the relevant consent — not before, not during the consent prompt itself.
This vendor review process is also a factor when evaluating the overall custom software development cost. Apps with complex third-party integration stacks require proportionally more compliance engineering work.
The 8-Point GDPR Compliance Checklist for App Developers
Use this checklist, a practical companion to this GDPR compliant app development guide, before submitting to app stores or launching in EU markets.
| S.No. | Compliance Requirement | Status |
| 1 | Privacy by Design implemented in architecture (GDPR Article 25) | ☐ |
| 2 | All data inputs and outputs are mapped in a Data Flow Diagram | ☐ |
| 3 | Data Minimization applied — only necessary data collected | ☐ |
| 4 | Granular, unbundled, active consent forms implemented | ☐ |
| 5 | Data encrypted in transit (TLS 1.2+) and at rest (AES-256) | ☐ |
| 6 | Users can view, export (CSV/JSON), and hard-delete their data | ☐ |
| 7 | All third-party SDKs audited and covered by signed DPAs | ☐ |
| 8 | 72-hour breach notification procedure documented and assigned | ☐ |
Intigate Technologies delivers compliance-by-design app development for healthcare, fintech, and e-commerce teams — with built-in consent management, user rights flows, and SDK audit protocols baked into every sprint.
Talk to Our Compliance-First Development Team →Conclusion
GDPR compliance in app development is not a legal checkbox; it is a product quality standard. With cumulative fines exceeding €7.1 billion and enforcement expanding beyond Big Tech into healthcare, fintech, and e-commerce, the risk of a non-compliant mobile app launch has never been higher.
The core insight from this GDPR compliant app development guide is architectural: compliance is substantially cheaper, faster, and more durable when designed in from the start rather than patched in after launch.
Privacy by Design, granular consent flows, hard-delete user rights features, and rigorous SDK audits are the four pillars that separate compliant apps from liability risks.
The Intigate Technologies development team is available to conduct compliance architecture reviews, gap assessments, and full-cycle GDPR-ready app builds across healthcare, fintech, and e-commerce verticals.
Forward this guide to your development team, or book a consultation to discuss your specific compliance roadmap.
FAQ: GDPR Compliant App Development
Does GDPR apply to apps built by companies outside the European Union?
Yes. GDPR applies to any organization that processes the personal data of EU residents, regardless of where the organization is based. Enforcement actions against US-based companies (including Clearview AI’s €30.5 million fine in 2024) confirm that geographic location provides no exemption from GDPR obligations.
What is the difference between Privacy by Design and a standard privacy policy?
A privacy policy is a legal document that describes how you process data. Privacy by Design (GDPR Article 25) is an architectural obligation: it requires data protection controls, such as encryption, data minimization, and access restrictions, to be embedded into system design before processing begins. A policy describes what you do; Privacy by Design determines how the system is built.
What is the Right to be Forgotten under GDPR, and how do developers implement it?
The Right to Erasure (GDPR Article 17) requires that a user’s personal data be permanently deleted upon request, not simply deactivated. Developers must build a hard-delete function that removes PII from production databases, clears cached copies, triggers deletion in third-party systems, and schedules removal from backup snapshots within a documented retention window.
Are third-party SDKs like Google Analytics or Facebook Pixel a GDPR risk for mobile apps?
Yes, and they are among the most common sources of GDPR violations in apps. Each SDK that collects or transmits personal data must be covered by a signed Data Processing Agreement with the vendor, and its initialization must be gated behind explicit user consent. Failing to do so makes the app developer jointly liable for any data the SDK collects without a valid legal basis.
How long does it take to build a GDPR-compliant mobile app from scratch?
Timeline varies by complexity, but compliance architecture adds roughly 15–25% to initial development scope when built correctly from day one. For a standard mHealth or fintech MVP, expect a compliance-ready build to take 4–6 months with a team experienced in privacy-by-design development. Retrofitting an existing non-compliant app takes longer and carries a higher risk — see how long it takes to build a Custom App for a detailed breakdown.



